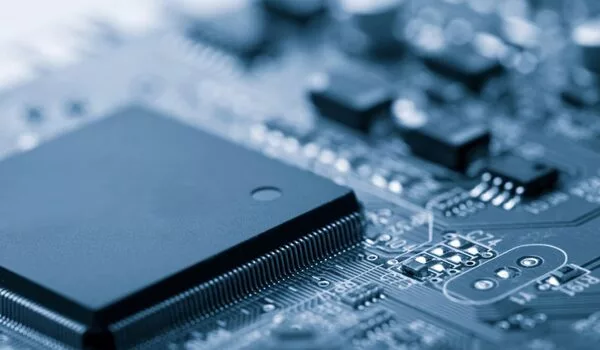
Two groundbreaking studies that describe how to engineer and improve the stability of ferroelectric hafnium oxides, which are compatible with common semiconductors, were published by members of a multifunctional thin film research group. Their work promotes semiconductor industry goals to reduce computing energy consumption by combining processing and memory components into a single integrated circuit.
The amount of energy used for computing is climbing at an exponential rate. Business intelligence and consulting firm Enerdata reports that information, communication, and technology accounts for 5% to 9% of total electricity consumption worldwide.
If growth continues unabated, computing could demand up to 20% of the world’s power generation by 2030. With power grids already under strain from weather-related events and the economy transitioning from fossil fuel to renewables, engineers desperately need to flatten computing’s energy demand curve.
Members of Jon Ihlefeld’s multifunctional thin film group are doing their part. They are investigating a material system that will allow the semiconductor industry to co-locate computation and memory on a single chip.
“Right now we have a computer chip that does its computing activities with a little bit of memory on it,” said Ihlefeld, associate professor of materials science and engineering and electrical and computer engineering at the University of Virginia School of Engineering and Applied Science.
Every time the computer chip wants to talk to memory the larger memory bank, it sends a signal down the line, and that requires energy. The longer the distance, the more energy it takes. Today the distance can be quite far – up to several centimeters.
“In a perfect world, we would get them in direct contact with each other,” Ihlefeld said.
The community had all sorts of explanations for why this is, and it turns out we were wrong. We thought the top electrode exerted some kind of mechanical stress, radiating laterally across the plane of the electrode, that prevented the hafnium oxide from stretching out and returning to its natural, non-ferroelectric state. My research shows that the mechanical stress moves out of plane; the electrode has a clamping effect.
Shelby Fields
That requires memory materials that are compatible with the rest of the integrated circuit. One class of materials suitable for memory devices are ferroelectrics, meaning they can hold and release a charge on demand. However, most ferroelectrics are incompatible with silicon and do not perform well when made very small, a necessity for modern-day and future miniaturized devices.
Researchers in Ihlefeld’s lab are playing matchmaker. Their research advances materials with electrical and optical properties that make modern computation and communication possible, a research strength of the Department of Materials Science and Engineering. They also specialize in fabrication and characterization of a range of materials, a research strength of the Charles L. Brown Department of Electrical and Computer Engineering.
Their material of interest is hafnium oxide, which is used in the manufacture of cell phones and computers today. The downside is that in its natural state, hafnium oxide is not ferroelectric.
A Tip of the Cap to Shelby Fields
Over the last 11 years, it has become known that hafnium oxide’s atoms can be manipulated to produce and hold a ferroelectric phase, or structure. When a hafnium oxide thin film is heated, a process called annealing, its atoms can move into the crystallographic pattern of a ferroelectric material; when the thin film is cooled, its crystalline structure sets in place.
Why formation of the ferroelectric phase happens has been the subject of much speculation. Shelby Fields, who earned a Ph.D. in materials science engineering from UVA this year, published a landmark study to explain how and why hafnium oxide forms into its useful, ferroelectric phase.
Fields’ paper, Origin of Ferroelectric Phase Stabilization via the Clamping Effect in Ferroelectric Hafnium Zirconium Oxide Thin Films, published in August in Advanced Electronic Materials, illustrates how to stabilize a hafnium oxide-based thin film when it is sandwiched between a metal substrate and an electrode. Previous research found that more of the film stabilizes in the ferroelectric crystalline phase when the top electrode is in place for thermal annealing and cooling.
“The community had all sorts of explanations for why this is, and it turns out we were wrong,” Fields said. “We thought the top electrode exerted some kind of mechanical stress, radiating laterally across the plane of the electrode, that prevented the hafnium oxide from stretching out and returning to its natural, non-ferroelectric state. My research shows that the mechanical stress moves out of plane; the electrode has a clamping effect.”
The whole sandwich – the substrate, thin film and electrode – is a capacitor, and this finding could very well alter the materials that semiconductor manufacturers select as electrodes.
“Now we understand why the top layer is such an important consideration. Down the line, people who want to integrate computing and memory on a single chip will have to think about all the processing steps more carefully,” Fields said.
Fields’ paper summarizes the concluding chapter of his dissertation research. In prior published research, Fields demonstrated techniques to measure very thin films and mechanical stresses; the miniscule materials made stress measurements experimentally difficult.
Contributors in this collaborative research include group members Samantha Jaszewski, Ale Salanova and Takanori Mimura as well as Wesley Cai and Brian Sheldon from Brown University, David Henry from Sandia National Labs, Kyle Kelley from Oak Ridge National Lab, and Helge Heinrich from UVA’s Nanoscale Materials Characterization Facility. Funding awarded through the U.S. Department of Energy’s 3D Ferroelectric Microelectronics Energy Frontier Research Center and the Semiconductor Research Corporation supported the research.
“We wanted to go beyond anecdotal descriptions and provide data to back up our characterization of the material’s behavior,” Fields said. “I am glad we could provide the community with greater clarity regarding this clamping effect. We know the top layer matters a lot and we can engineer that top layer to improve the clamping effect, and perhaps engineer the bottom layer to help with this effect, too. The ability to leverage a single experimental variable to control the crystalline phase would be a huge advantage for the semiconductor field. I would love for someone to ask and answer that question.”
O Marks the Spot
That someone could be Samantha Jaszewski, a Ph.D. student of materials science and engineering and a member of Ihlefeld’s Multifunctional Thin Film research group. Jaszewski also wants to understand what contributes to the stability of hafnium oxide’s ferroelectric phase and how chip designers can control the material’s behavior.
Jaszewski’s research focuses on the atomic make-up of hafnium oxide in its natural and ferroelectric phase, with specific attention on the role of oxygen atoms. Her landmark study, Impact of Oxygen Content on Phase Constitution and Ferroelectric Behavior of Hafnium Oxide Thin Films Deposited by Reactive High-Power Impulse Magnetron Sputtering, is published in the October 2022 issue of Acta Materialia.
Hafnium oxide, as the name suggests, is composed of hafnium and oxygen atoms. “Sometimes we are missing those oxygen atoms in certain places, and that helps stabilize the ferroelectric phase,” Jaszewski said.
The natural, non-ferroelectric state can tolerate a number of these oxygen vacancies, but not as many as needed to stabilize the ferroelectric phase. The precise concentration and location of oxygen vacancies that makes hafnium oxide ferroelectric has proven elusive because there aren’t many tools available to make a definitive measurement.
Jaszewski worked around that problem by using several different techniques to measure oxygen vacancies in the team’s thin films and correlated that with ferroelectric properties. She discovered that the ferroelectric phase requires a much higher number of oxygen vacancies than previously thought.
X-ray photoelectron spectroscopy was the go-to tool to calculate oxygen vacancy concentrations. Jaszewski discovered that there are contributing factors beyond what users of this spectroscopy technique typically measure, leading to a vast undercount of oxygen vacancies.
Jaszewski’s experiments also reveal that oxygen vacancies may be one of, if not the, most important parameters to stabilize the ferroelectric phase of the material. More research needs to be done to understand how the vacancies exist. She would also like to have other research teams measure the oxygen vacancies using her method to validate her findings.
Jaszewski’s research overturns conventional wisdom, which suggested that the size of the crystal – called a grain – is what stabilizes the hafnium oxide. Jaszewski made three samples with equal grain sizes and different oxygen vacancy concentrations. Her research shows that the phases present in these samples varied, leading to the conclusion that oxygen vacancy concentration is more important than grain size.
Jaszewski first-authored the paper, which was co-authored by group members Fields and Salanova with collaborators in many research groups within and outside of UVA. Jaszewski’s research is funded by her National Science Foundation graduate research fellowship and the Semiconductor Research Corporation.
Jaszewski is deepening her inquiry into hafnium oxides to explain the material’s response to the application of an electric field. In the semiconductor industry, this phenomenon is referred to as wake-up and fatigue.
“When you apply an electric field to this material, the ferroelectric properties increase, or ‘wake-up.’ As you continue to apply the electric field, the ferroelectric properties degrade, in a process known as fatigue,” Jaszewski said. She has found that when an electric field is initially applied, it boosts the ferroelectric structure, but there are diminishing returns.
“As you continue to apply the field the ferroelectric properties degrade,” Jaszewski said. The next step is investigating how the oxygen atoms’ choreography in the material contributes to wake-up and fatigue, which requires study of where vacancies are located dynamically.
“These landmark studies explain why ferroelectric hafnium oxide exists and how it stabilizes,” Ihlefeld said. “Based on these new findings, we can engineer hafnium oxide thin films to be even more stable and perform even better in an actual application. By doing this fundamental research we can help semiconductor firms understand the origin of problems and how to prevent them in future production lines.”